Settings
The settings page is where operators define how ainative-business authenticates, which tool requests can be trusted by default, how much provider activity is allowed to cost, and how the local workspace data should be managed.
The Settings page is the central configuration hub for ainative-business. From a single scrollable page you can manage authentication for all provider runtimes, tune agent execution parameters, configure local AI models via Ollama and browser automation, set monthly cost caps, choose permission presets, manage delivery channels for Slack and Telegram, schedule database snapshots, and reset workspace data. Each section saves changes immediately with confirmation feedback, and a sticky table of contents on the left lets you jump between sections without scrolling.
Screenshots
 Settings landing area showing the section index and the first configuration cards.
Settings landing area showing the section index and the first configuration cards.
 The full settings page captured end-to-end — every configurable section visible in one scroll.
The full settings page captured end-to-end — every configurable section visible in one scroll.
Key Features
Authentication
 Authentication card with Anthropic OAuth/API key choice, OpenAI Codex key/ChatGPT sign-in, and per-runtime connection tests.
Authentication card with Anthropic OAuth/API key choice, OpenAI Codex key/ChatGPT sign-in, and per-runtime connection tests.
Choose how ainative-business connects to each provider runtime. For Anthropic, OAuth uses your existing Max subscription at no additional API cost, while API Key uses the Anthropic key stored in your environment. For OpenAI, Codex App Server can use either an OpenAI API key or ChatGPT browser sign-in, while OpenAI Direct continues to use an API key. Connection tests validate the currently selected runtime mode and the OpenAI section shows active ChatGPT account and Codex rate-limit state when available.
Runtime Configuration
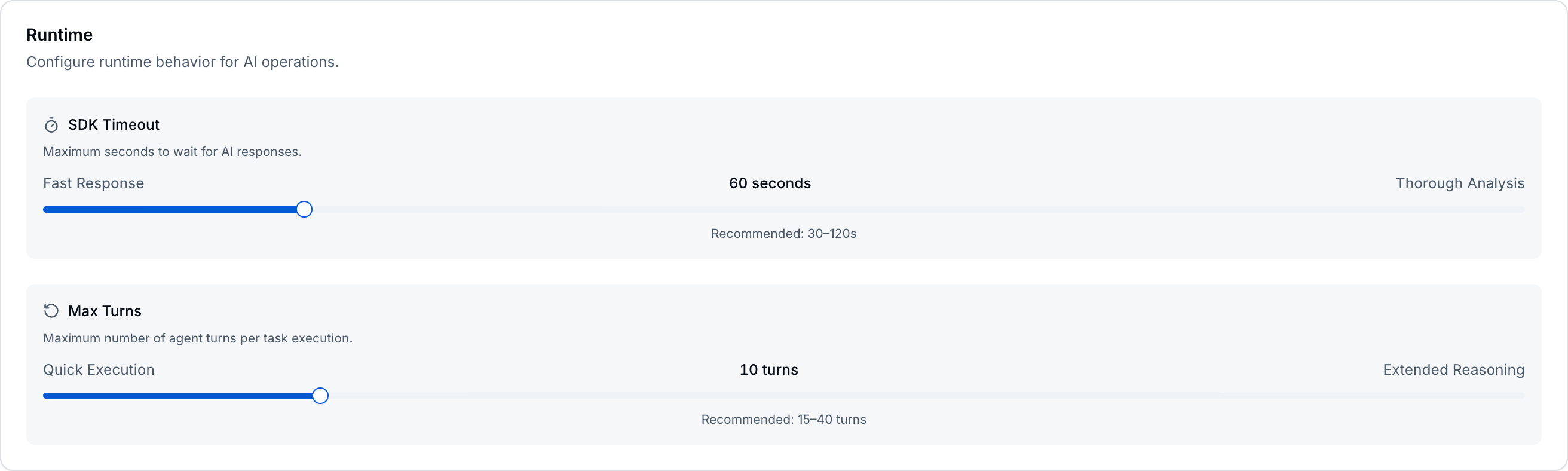 Runtime card grouping SDK timeout, max turns, Ollama connection, and the Chrome DevTools / Playwright browser toggles.
Runtime card grouping SDK timeout, max turns, Ollama connection, and the Chrome DevTools / Playwright browser toggles.
The Runtime card consolidates execution-environment controls into one place:
- SDK Timeout — how many seconds an individual agent call is allowed to run before timing out. Lower values return faster; higher values give the agent more time for complex reasoning.
- Max Turns — how many back-and-forth tool-use cycles the agent can perform in a single run. Fewer turns suit quick lookups; more turns allow extended multi-step work.
- Ollama — connect to a local Ollama instance for private, zero-cost AI execution. The card shows connection status, the discovered local model list (with name, size, last-modified date), and a Test Connection button. Once connected, Ollama models appear as runtime options throughout the workspace and tasks routed to Ollama are tracked at $0 in the cost dashboard.
- Browser Tools — two independent toggles enable browser automation. Chrome DevTools connects to a running Chrome window (debug your own app, inspect network traffic, run performance audits, take screenshots of live pages). Playwright launches its own headless browser (autonomous web research, page scraping, structured analysis, cross-browser testing). When enabled, read-only actions auto-approve; state-changing actions still go through the permission flow.
Chat Defaults
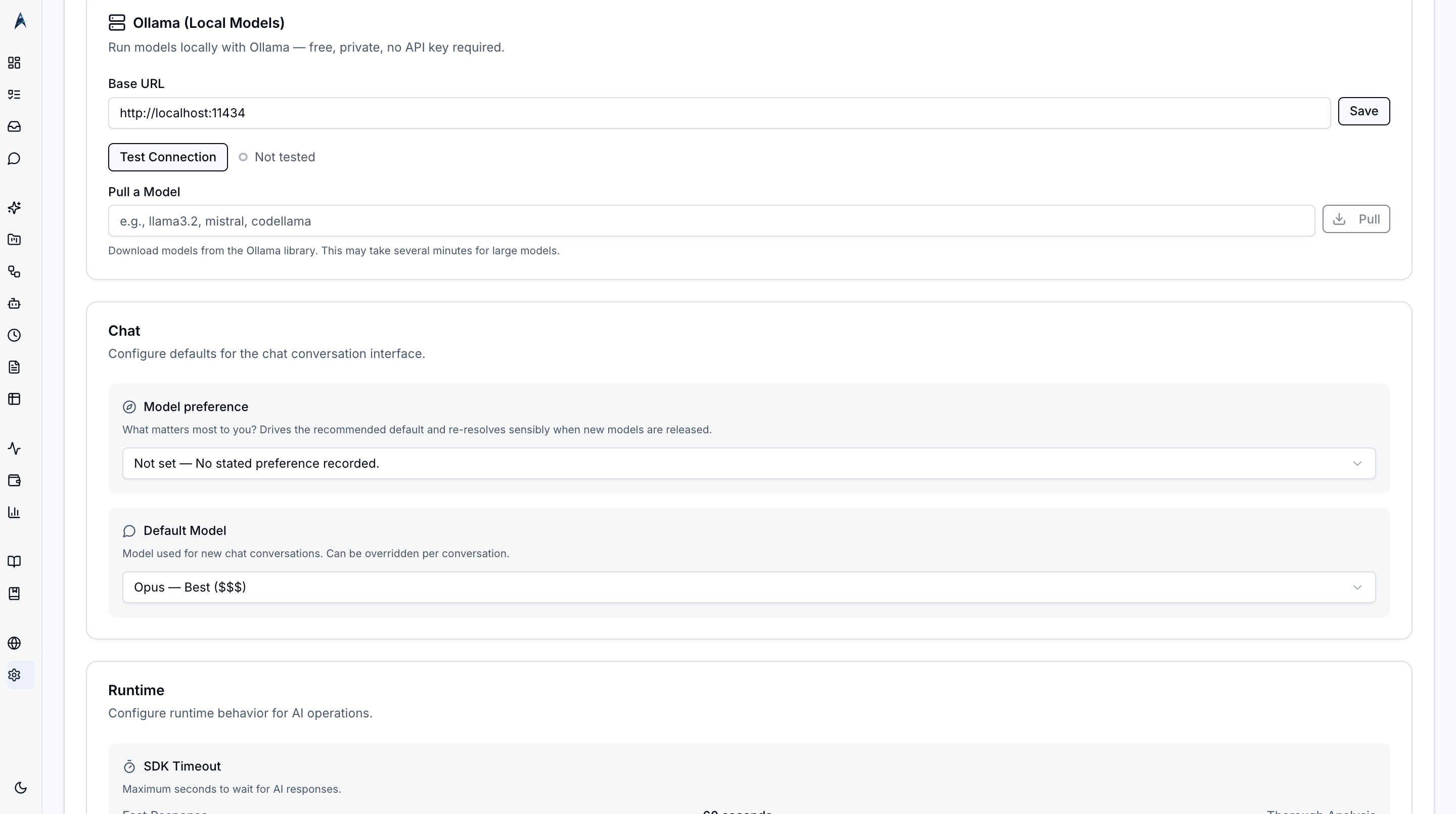 Chat default model picker showing Claude, Codex, and Ollama options grouped by provider with cost tiers.
Chat default model picker showing Claude, Codex, and Ollama options grouped by provider with cost tiers.
Pick the default model for new chat conversations. The selector shows available Claude, Codex, and Ollama models with relative cost tiers so you can balance capability against spend before starting a conversation. The picker is the same one used in the chat composer; changing it here only updates the default for new conversations — existing conversations keep their selected model.
Delivery Channels
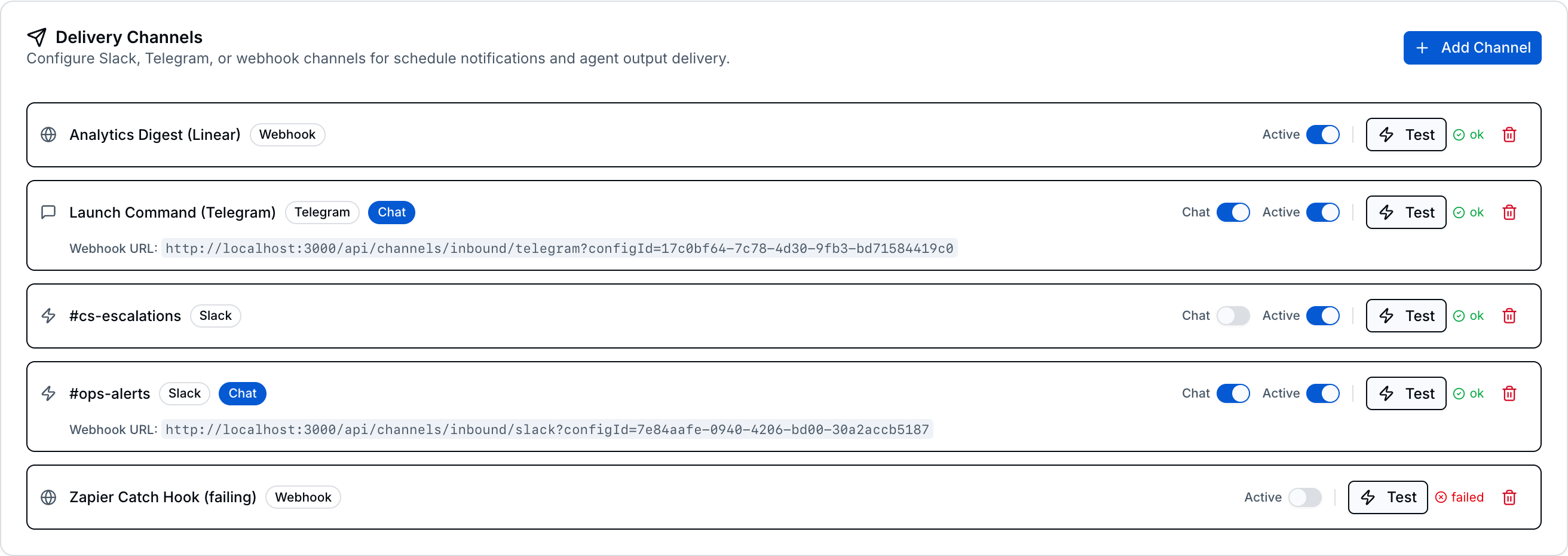 Delivery Channels card showing configured Slack, Telegram, and webhook integrations with Chat mode and Active toggles.
Delivery Channels card showing configured Slack, Telegram, and webhook integrations with Chat mode and Active toggles.
Configure external messaging integrations for outbound notifications and bidirectional chat:
- Slack — connect via webhook URL for notifications, or add a bot token for bidirectional chat directly from Slack.
- Telegram — connect via bot token for both notifications and bidirectional chat.
- Webhook — send notifications to any HTTP endpoint (outbound only).
Each channel card has four controls: a Chat toggle for bidirectional mode (Slack and Telegram only), an Active toggle, a Test button, and a Delete button. When Chat is enabled, you can message ainative-business directly from Slack or Telegram and receive AI responses in the same conversation. See the Delivery Channels guide for detailed setup instructions.
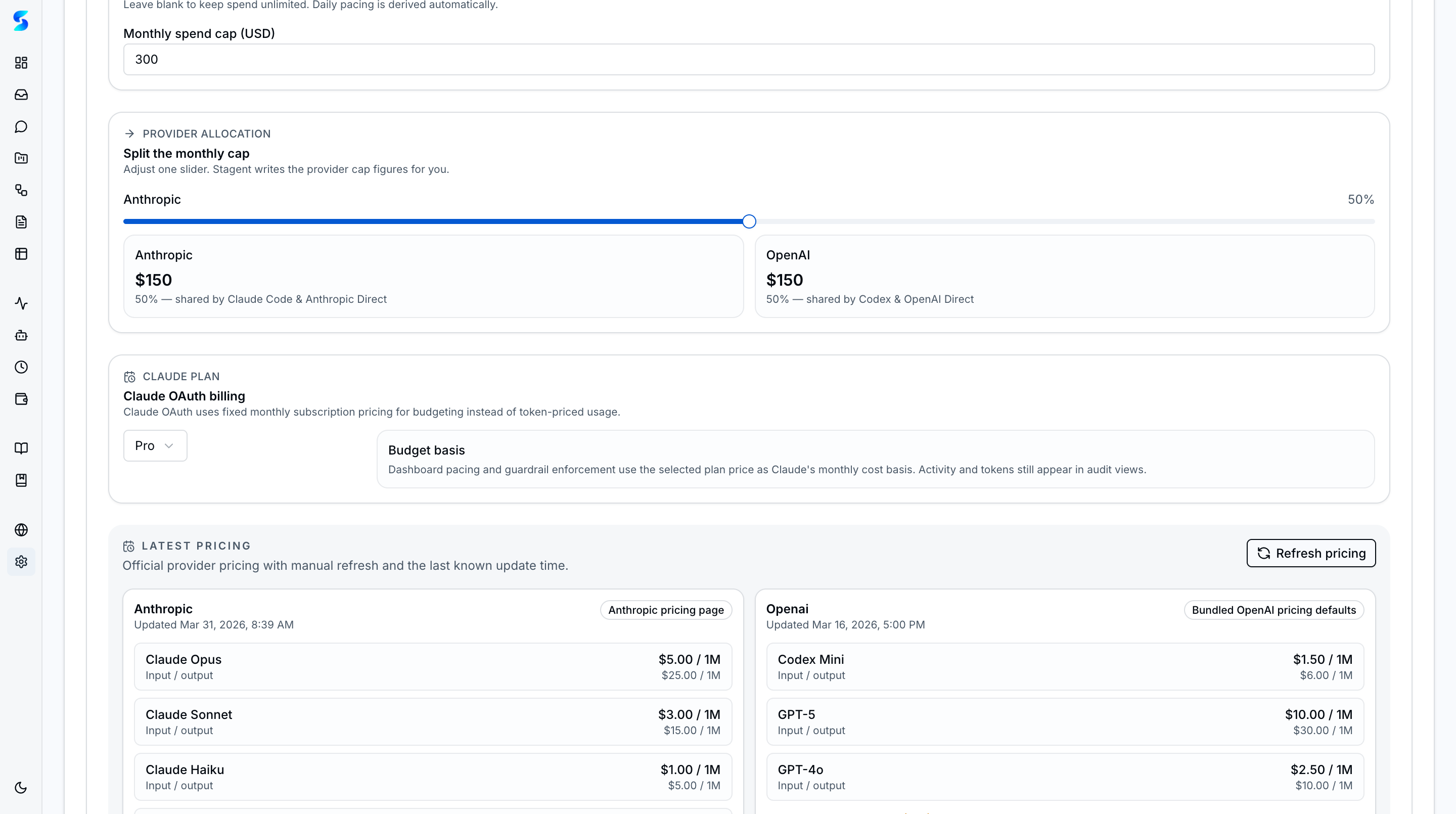
Cost and Usage Guardrails
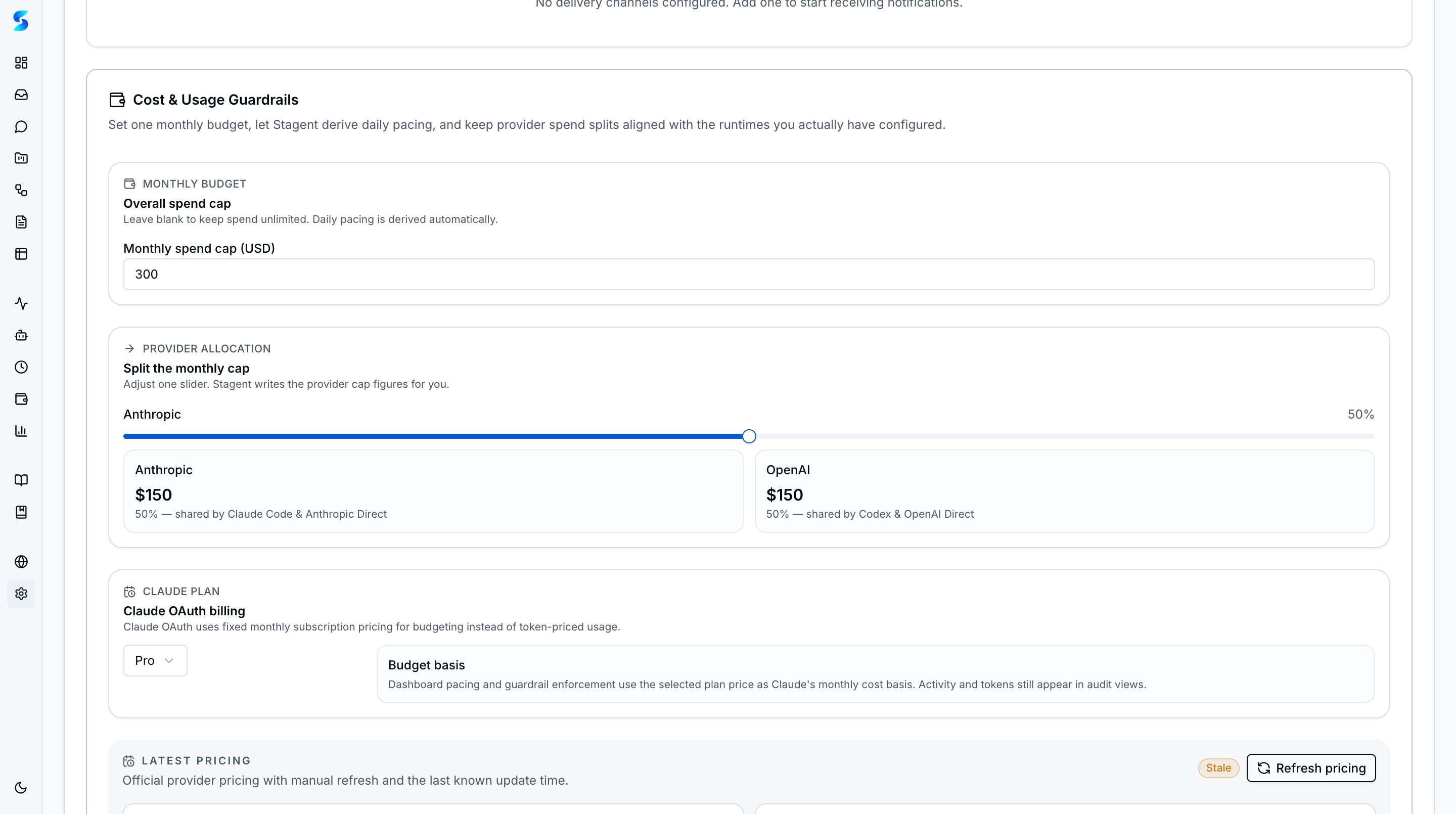 Cost and Usage Guardrails with overall spend cap, monthly split, billing indicator, and pacing meter.
Cost and Usage Guardrails with overall spend cap, monthly split, billing indicator, and pacing meter.
Set spend caps to prevent runaway costs from autonomous agent work:
- Overall spend cap — a hard monthly ceiling across all providers.
- Monthly split — distribute the budget across billing periods.
- Per-provider caps — optional daily and monthly limits for Claude, Codex, and other providers independently.
A pacing meter shows current spend against the cap with color-coded health (green, amber, red). When usage crosses 80% of a configured cap an inbox notification is sent. After the cap is exceeded, new agent work is blocked.
Permission Presets
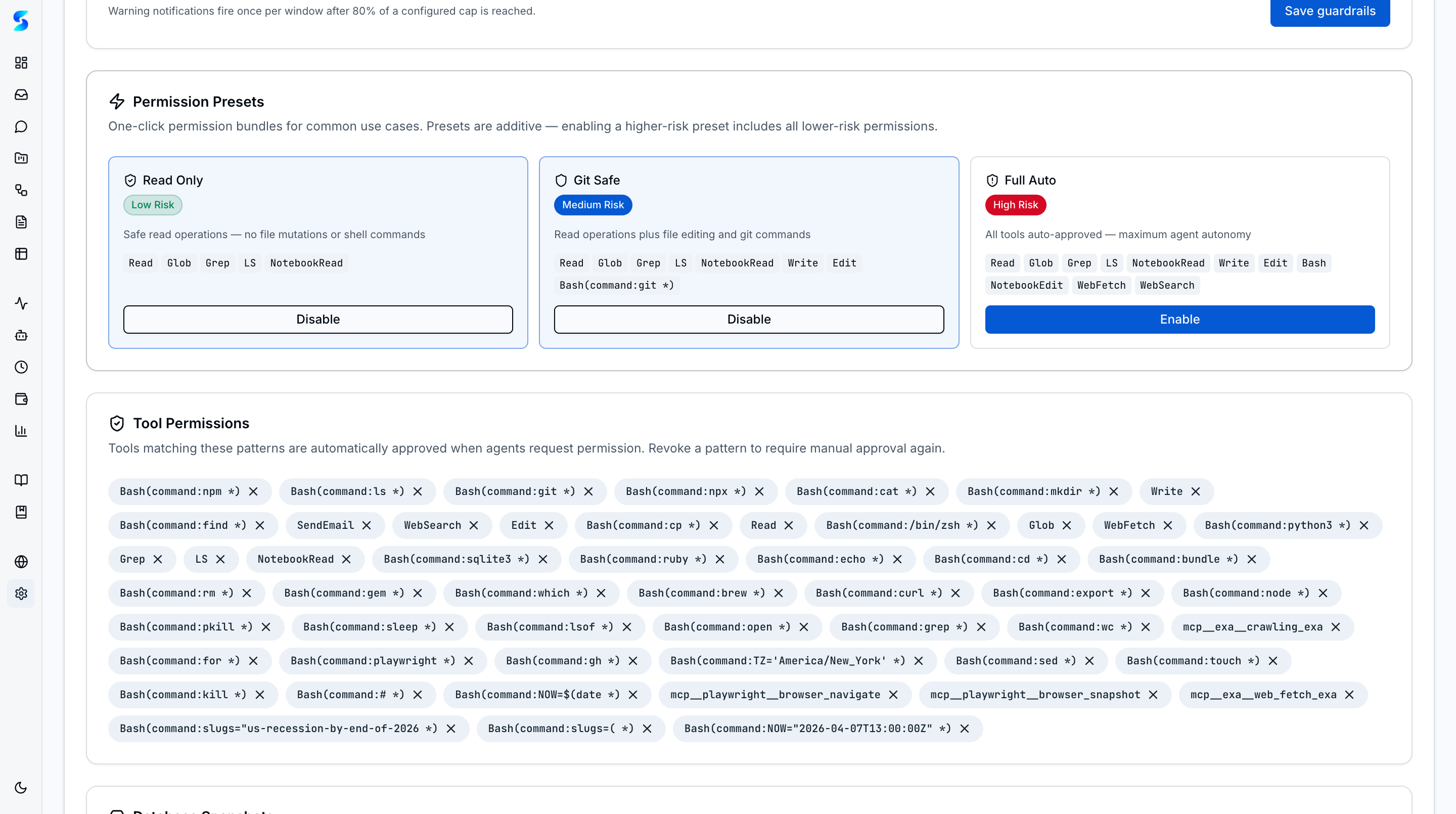 Permission Presets card with Read Only, Git Safe, and Full Auto tiers, color-coded risk badges, and individual toggles.
Permission Presets card with Read Only, Git Safe, and Full Auto tiers, color-coded risk badges, and individual toggles.
Three one-click bundles set tool permissions in bulk:
| Preset | What it allows | Risk |
|---|---|---|
| Read Only | File reading, search, directory listing | Lowest |
| Git Safe | Everything in Read Only plus file edits and git commands | Medium |
| Full Auto | All tools except direct user questions | Highest |
Presets are additive — enabling Git Safe automatically includes Read Only tools. Disabling a preset removes only its unique additions without affecting tools you approved individually.
Tool Permissions
 Persisted tool-permission list with each pattern, the granting preset (if any), and a per-row Revoke button.
Persisted tool-permission list with each pattern, the granting preset (if any), and a per-row Revoke button.
Below the presets, a list shows every individually approved tool pattern. Patterns follow the format used by Claude Code (e.g., Bash(git:*), Read(/src/**)). Each pattern has a Revoke button. The special AskUserQuestion tool is never auto-approved regardless of presets — it always renders an interactive reply field in the inbox.
Database Snapshots
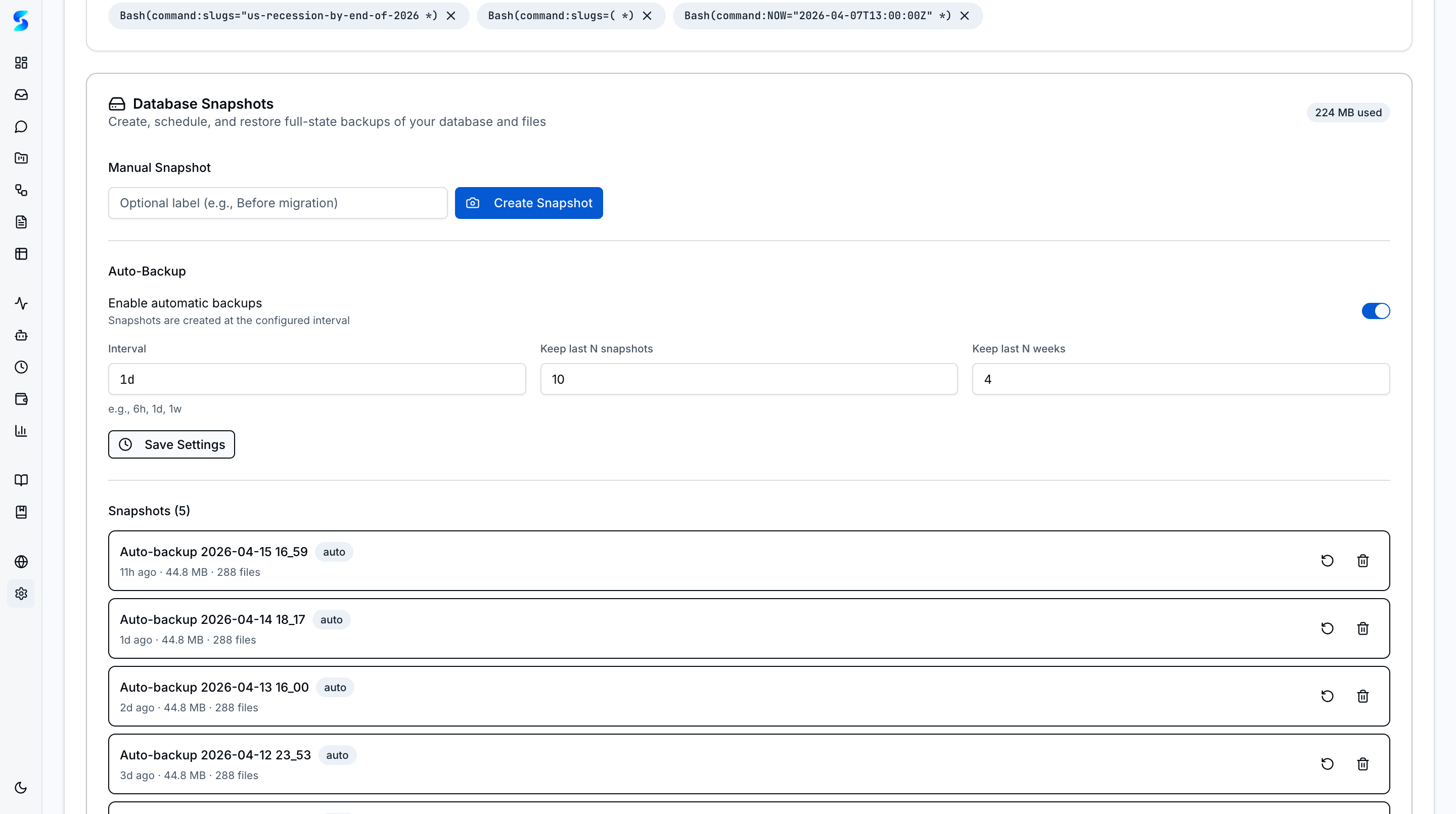 Database Snapshots card with automatic backup configuration, retention settings, and snapshot list with restore/delete actions.
Database Snapshots card with automatic backup configuration, retention settings, and snapshot list with restore/delete actions.
Protect your workspace with automatic and manual database backups:
- Automatic backup — enable scheduled backups with a configurable cron interval (e.g., every 6 hours, daily). Snapshots are created in the background without interrupting your workflow.
- Retention settings — control how many snapshots to keep with a maximum count and a maximum age in weeks. Older snapshots beyond the retention limits are pruned automatically.
- Snapshot list — view all existing snapshots with timestamps and sizes. Each snapshot has Restore and Delete action buttons for quick management.
- Pre-restore safety snapshot — before restoring an older snapshot,
ainative-businessautomatically creates a safety snapshot of the current database state so you can roll back if needed.
Data Management
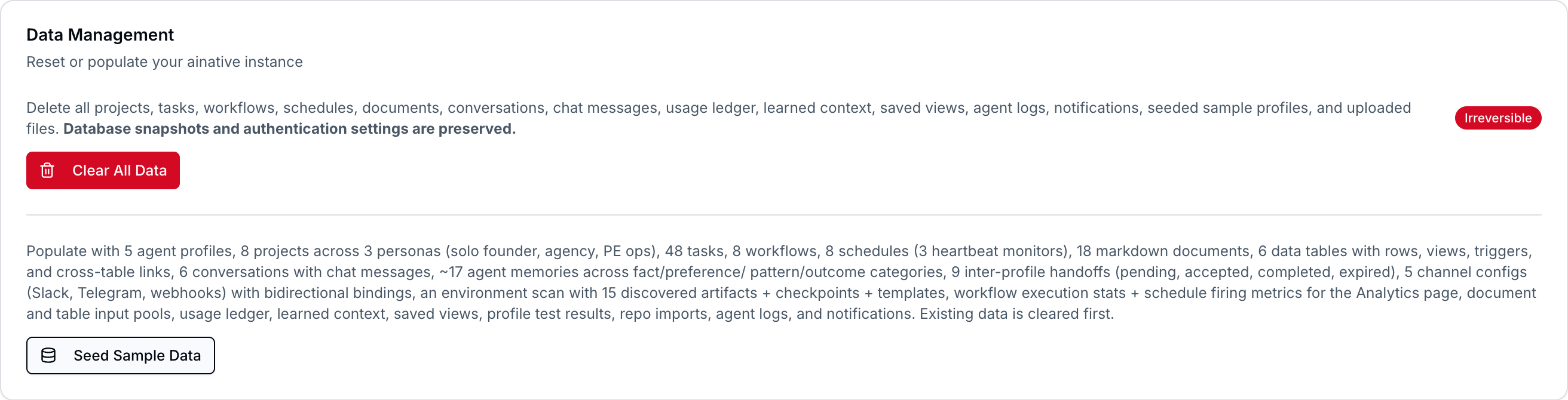 Data Management card with Clear Data and Populate Sample Data actions.
Data Management card with Clear Data and Populate Sample Data actions.
Two operations for managing workspace content:
- Clear Data — removes tasks, logs, documents, schedules, and other workspace content. Settings and permissions are preserved.
- Populate Sample Data — seeds the workspace with example projects, tasks, and documents so you can explore features against realistic data.
Instance & Upgrades
 The Instance section shows the installation metadata and the upgrade flow entry point.
The Instance section shows the installation metadata and the upgrade flow entry point.
Instance Section
The Instance card surfaces metadata about this installation: the stable instanceId, the current instance branch (e.g., local for single-clone users, wealth-mgr for private instances), the upstream remote it tracks, and whether the first-boot bootstrap has completed. Power users also see the guardrail state — whether a pre-push hook is installed and whether pushRemote=no_push is set on the instance branch.
Dev Mode Gate
When AINATIVE_DEV_MODE=true is set in .env.local or the .git/ainative-dev-mode sentinel file is present, the Instance section displays a “Dev mode” banner and the upgrade machinery is intentionally bypassed. This is the gate that protects the main dev repo from having a pre-push hook installed by the instance-bootstrap flow — contributors working on ainative-business itself must not have their own push workflow broken.
Upgrade Detection
An hourly scheduled poll runs git fetch against the upstream remote and compares HEAD to origin/main. When upstream is ahead, the sidebar shows a small Upgrade available badge next to Settings and the Instance card surfaces a “New version available” card with the number of commits behind. Detection is git-based rather than GitHub REST to avoid rate limits. Three consecutive poll failures escalate to a persistent notification.
Upgrade Session
Clicking Start upgrade opens the upgrade session as a right-side sheet — not a full-page navigation, so you can glance back at your workspace while the upgrade runs. The session is backed by a task row with the upgrade-assistant profile, so it reuses all the existing execution infrastructure: fire-and-forget launch, canUseTool approval caching, SSE log streaming, and conflict resolution via the pending-approval host. If merge conflicts occur, a 3-card cluster (Keep mine / Take theirs / Show diff) appears inline and you resolve them without leaving the sheet. When the assistant needs a direct answer (e.g., to disambiguate a conflict), it now calls AskUserQuestion, which renders a typed reply field via the inbox’s QuestionReplyActions branch — you answer in-place and the assistant resumes. The upgrade-assistant profile explicitly allowlists AskUserQuestion so it is not gated behind a generic permission prompt.
Footer Upgrade Button
A subtle Upgrade button appears in the sidebar footer once an upgrade is available — the same surface that shows trust tier and the command palette shortcut. Clicking it opens the same upgrade session sheet from any page without navigating to Settings first.
Hybrid Licensing
Local-only features (task execution, workflows, schedules, tables) remain unlimited regardless of license state. Cloud features (sync, marketplace, team sharing) are metered via a (email, machineFingerprint, instanceId) tuple so the same user on the same machine counts as one seat across multiple instance branches. Seat state is refreshed on each boot via the LicenseManager.
How To
Connect Ollama for Local Models
- Install Ollama from ollama.com and pull at least one model (e.g.,
ollama pull llama3). - Open Settings and scroll to the Runtime section.
- Verify the Ollama URL (default:
http://localhost:11434). - Click Test Connection — the status should show “Connected” with a list of available models.
- Once connected, Ollama models appear in runtime selectors across the workspace.
Switch Anthropic from API Key to OAuth
- Scroll to the Authentication section.
- Under Anthropic, select OAuth.
- Click Sign in with Anthropic — a browser window opens to claim a token from your Max subscription.
- After consent, the connection test runs automatically. New tasks now use OAuth (no per-call API charges).
Add a Delivery Channel
- Scroll to the Delivery Channels section in Settings.
- Click + Add Channel.
- Select the channel type (Slack, Telegram, or Webhook).
- Enter the required configuration fields (see the Delivery Channels guide for per-type details).
- Click Create Channel, then Test to verify connectivity.
- Toggle Chat on for bidirectional mode (Slack and Telegram only).
Enable Browser Automation
- Scroll to the Runtime section.
- In the Browser Tools subgroup, toggle Chrome DevTools on for debugging live pages, or Playwright for headless automation.
- Both can be enabled simultaneously. Changes take effect immediately.
Set a Monthly Budget
- Scroll to Cost & Usage Guardrails.
- Enter an overall monthly spend cap.
- Optionally set per-provider caps for finer control.
- Watch the pacing meter throughout the month.
Configure Permission Presets
- Scroll to Permission Presets.
- Toggle on the preset that matches your comfort level.
- The preset’s tools are added to your approved list immediately and appear in the Tool Permissions list below.
Schedule Automatic Database Snapshots
- Scroll to Database Snapshots.
- Toggle Automatic backup on and choose a cron interval (e.g., every 6 hours).
- Set retention: maximum count and maximum age in weeks.
- New snapshots run on the schedule. Click Snapshot now for an on-demand backup.
Related
Related Features
- Agent Integration — Uses the configured API key
- Cost & Usage — Budget guardrails and cross-runtime usage visibility
- Home & Dashboard — Reflects current workspace state
- Documents — Upload storage configuration